AWS Security Hub scanner reference for STO
You can scan your configurations and ingest the scan results from AWS Security Hub.
Important notes for running AWS Security Hub scans in STO
-
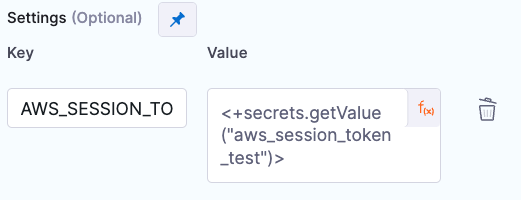
This integration supports session-based authentication with AWS. You can pass the token as a key-value pair in the Settings field.
-
If you want to add trusted certificates to your scan images at runtime, you need to run the scan step with root access.
-
You can set up your STO scan images and pipelines to run scans as non-root and establish trust for your own proxies using custom certificates. For more information, go to Configure STO to Download Images from a Private Registry.
The following topics contain useful information for setting up scanner integrations in STO:
AWS Security Hub step configuration
The default workflow is to add an AWS Security Hub step to a Build or Security stage and configure it as described below.
Scan
Scan Mode
- Extraction Configure the step to extract scan results from an external SaaS service and then ingest, normalize, and deduplicate the data.
- Ingestion Configure the step to read scan results from a data file and then ingest, normalize, and deduplicate the data.
Scan Configuration
The predefined configuration to use for the scan. All scan steps have at least one configuration.
Target
Type
- Instance Scan a running application.
- Configuration Scan your cloud environment by gathering configuration data via the cloud provider’s APIs.
Name
The identifier for the target, such as codebaseAlpha or jsmith/myalphaservice. Descriptive target names make it much easier to navigate your scan data in the STO UI.
It is good practice to specify a baseline for every target.
Variant
The identifier for the specific variant to scan. This is usually the branch name, image tag, or product version. Harness maintains a historical trend for each variant.
Ingestion File
The path to your scan results when running an Ingestion scan, for example /shared/scan_results/myscan.latest.sarif.
-
The data file must be in a supported format for the scanner.
-
The data file must be accessible to the scan step. It's good practice to save your results files to a shared path in your stage. In the visual editor, go to the stage where you're running the scan. Then go to Overview > Shared Paths. You can also add the path to the YAML stage definition like this:
- stage:
spec:
sharedPaths:
- /shared/scan_results
Authentication
You should create Harness text secrets with your encrypted access ID and token and access them using the format <+secrets.getValue("my-secret")>.
Access ID
The access ID for your AWS account.
Access Token
The access token for your AWS account.
Access Region
Your AWS region.
Log Level
The minimum severity of the messages you want to include in your scan logs. You can specify one of the following:
- DEBUG
- INFO
- WARNING
- ERROR
Fail on Severity
Every Custom Scan step has a Fail on Severity setting. If the scan finds any vulnerability with the specified severity level or higher, the pipeline fails automatically. You can specify one of the following:
CRITICALHIGHMEDIUMLOWINFONONE— Do not fail on severity
The YAML definition looks like this: fail_on_severity : critical # | high | medium | low | info | none
Settings
You can use this to add environment variables to your scan environment. To enable session-based authentication with AWS, for example, you can pass AWS_SESSION_TOKEN with a Harness text secret of your token.